- Introduction to STP Root Bridge Election
- What is Root Bridge in STP?
- Understanding Root Bridge ID
- STP Root Bridge Election Priority
- STP Election Process Step by Step
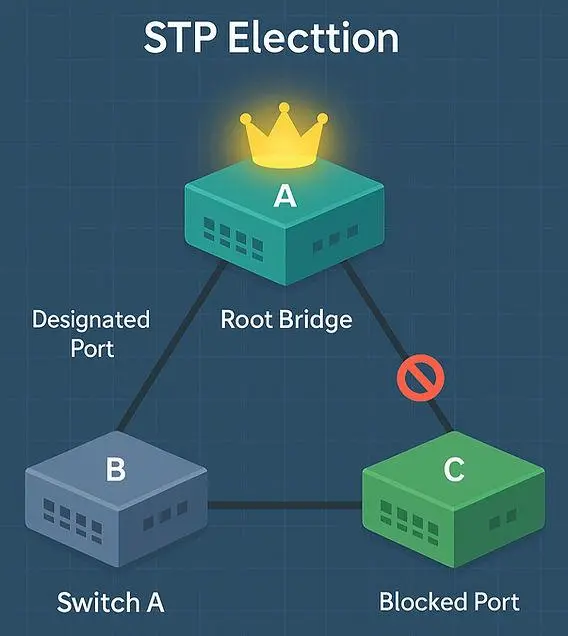
- Step-by-Step Example with 3 Switches
- Root Port Election in STP
- Real-World Scenario
- Common Mistakes in STP Election
- Advanced Networking Context
- Broader Networking Concepts
- Security & Threat Awareness
- Conclusion
- FAQs
Introduction to STP Root Bridge Election
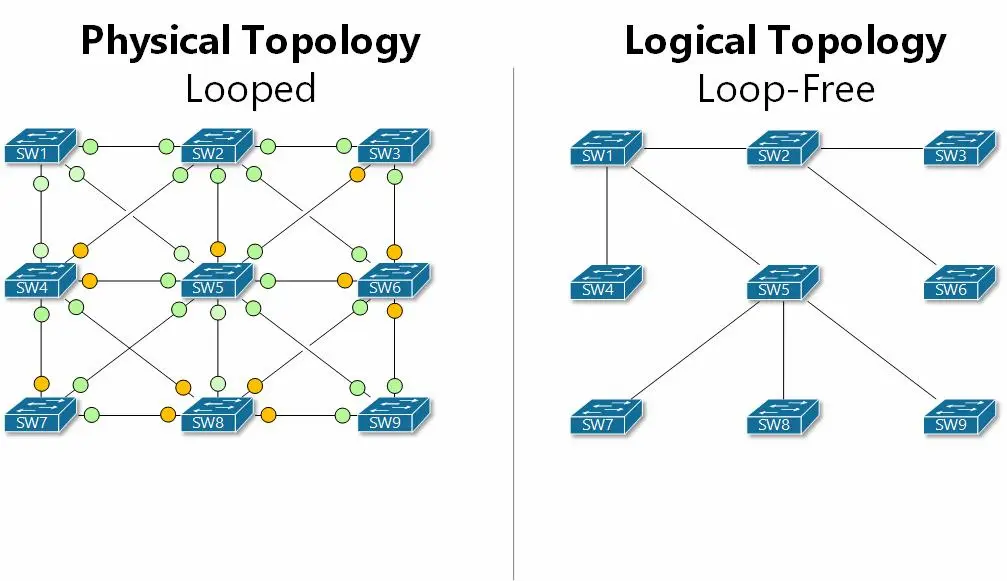
In modern networks, redundancy is essential to ensure high availability. However, redundant links can create network loops, leading to broadcast storms, duplicate frames, and serious performance issues.
This is where Spanning Tree Protocol (STP) comes in. STP prevents loops by creating a loop-free topology and selecting one switch as the Root Bridge, which becomes the central reference point for all traffic decisions.
Understanding an STP Root Bridge Election Example helps you clearly see how switches decide leadership within a network.
👉 Experience Insight:
In real-world environments, I’ve seen entire networks go down due to improper STP configuration. In most cases, the issue was not STP itself, but incorrect root bridge selection.
Before diving into the detailed explanation, it’s helpful to first understand how STP root bridge election works in a real network. The short video below gives you a clear visual example of how switches compare priority and MAC address to select the root bridge.
Now that you’ve seen a practical example, let’s break down the STP root bridge election process step by step and understand how each decision is made inside the network.
STP prevents network loops by blocking redundant paths and creating a stable topology.
What is Root Bridge in STP?
The Root Bridge is the main switch in an STP-enabled network. All other switches calculate the best path to reach it.
It controls:
- Traffic flow direction
- Port states (forwarding or blocking)
- Overall network stability
👉 Experience Insight:
In enterprise networks, the root bridge is typically placed on a core switch. If an access switch becomes the root bridge by mistake, it can lead to inefficient traffic flow and degraded performance.
To understand the process in detail, see:
STP root bridge election process explained
For external reference:
Flackbox STP Root Bridge Guide
Understanding Root Bridge ID
The Root Bridge is selected based on the Bridge ID (BID).
Components:
- Bridge Priority
- MAC Address
Bridge ID consists of priority and MAC address, which determines the root bridge.
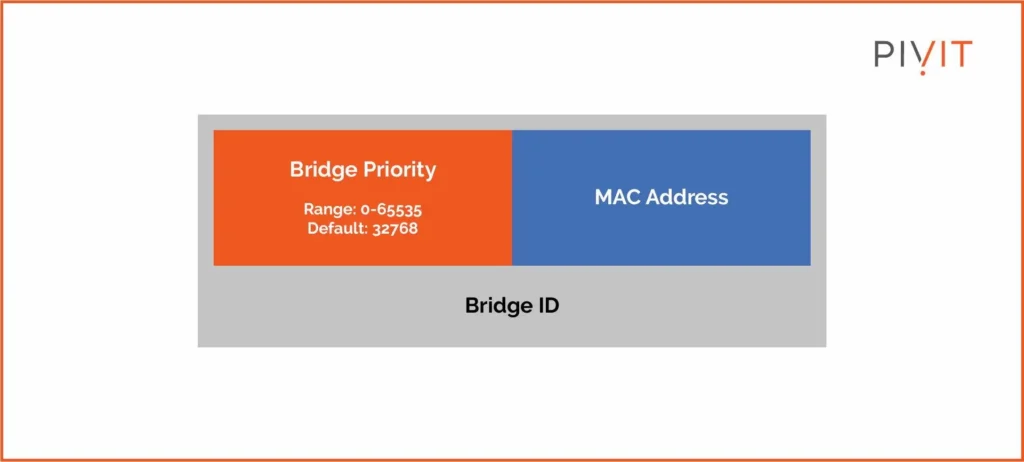
Formula:
Bridge ID = Priority + MAC Address
👉 The switch with the lowest Bridge ID becomes the Root Bridge.
👉 Experience Insight:
During troubleshooting, checking the Bridge ID is often the fastest way to understand why a particular switch was selected as the root.
For deeper understanding:
Bridge ID in STP priority and MAC address
STP Root Bridge Election Priority
- Default Priority = 32768
- Range = 0–65535
- Lower value = higher priority
👉 If priorities are equal, the MAC address determines the root bridge.
👉 Experience Insight:
Many beginners leave the priority at default, allowing the MAC address to decide the root bridge. This removes control from network design and can lead to unexpected results.
For algorithm-level understanding:
NetworkAcademy STP Algorithm
STP elects the root bridge by comparing priority first and then MAC address.
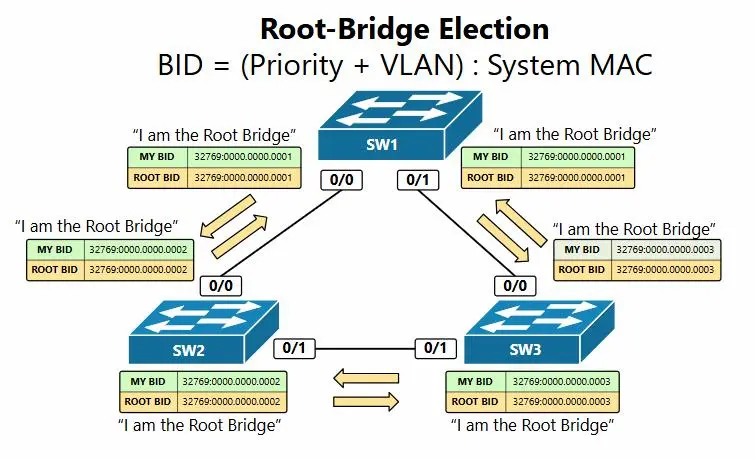
STP Election Process Step by Step
Step 1: Compare Bridge Priority
Step 2: Compare MAC Address
Step 3: The switch with the lowest Bridge ID becomes the Root Bridge
👉 This simple logic determines the hierarchy of the network.
👉 Experience Insight:
In production environments, engineers never rely on default election. They manually configure priorities to ensure predictable and stable behavior.
For additional explanation:
GeeksforGeeks STP Election
Step-by-Step Example with 3 Switches
Network Setup:
| Switch | Priority | MAC Address |
|---|---|---|
| SW1 | 32768 | 00:11:22:33:44:55 |
| SW2 | 32768 | 00:11:22:33:44:11 |
| SW3 | 24576 | 00:11:22:33:44:99 |
Step 1: Compare Priority
SW3 has the lowest priority → wins immediately
Step 2: MAC Comparison (if needed)
Final Result:
👉 SW3 becomes the Root Bridge
👉 Experience Insight:
In real deployments, engineers predefine which switch should become the root instead of leaving it to automatic selection.
In a three-switch network, the switch with the lowest Bridge ID becomes the root bridge.
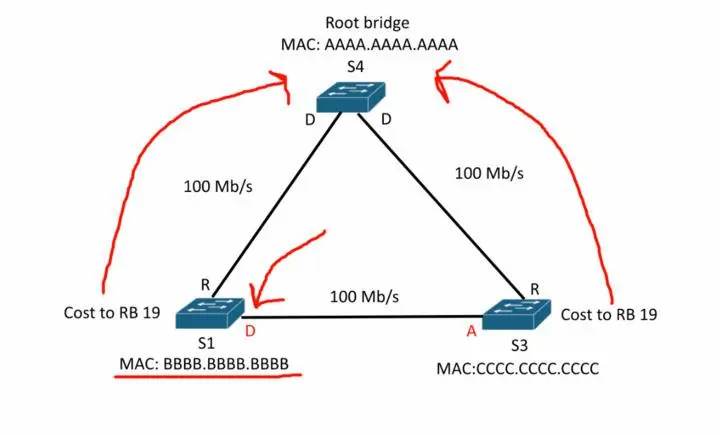
Root Port Election in STP
After the root bridge is selected, each switch chooses its Root Port.
The root port is the port with the lowest cost path to the root bridge.
Selection Criteria:
- Lowest path cost
- Lowest upstream Bridge ID
- Lowest port ID
👉 Experience Insight:
Correct root port selection ensures efficient traffic flow and reduces latency in large-scale networks.
For more details:
NWKINGS STP Election Process
Root ports are selected based on the lowest cost path to the root bridge.
Real-World Scenario
In enterprise networks:
- Core switches are configured as root bridges
- Access switches should not become root
If not configured properly:
👉 An access switch may become the root bridge
👉 Traffic flow becomes inefficient
👉 Author Insight:
From experience, STP planning is often ignored during initial setup. However, it becomes critical as the network grows and redundancy increases.
For network security context:
how firewalls protect networks
FortiGate 100F firewall
Common Mistakes in STP Election
- Leaving default priority unchanged
- Not configuring a backup root bridge
- Ignoring proper network design
- Misunderstanding Bridge ID
👉 Experience Insight:
Most STP-related issues are caused by poor planning rather than technical complexity.
For security awareness:
dangerous passwords
weak file permissions
Advanced Networking Context
Modern networks go beyond switching.
They also include:
- Wireless security
- Authentication protocols
- API security
Explore more:
enterprise WiFi security risks
802.1X authentication
API security
Broader Networking Concepts
STP is just one part of networking.
You can explore:
FastEthernet0 explained
PVST election process
stateful switchover
DMVPN scalability
Security & Threat Awareness
Network design must also consider security threats.
Explore:
file upload vulnerability
BEAST attack
reverse engineering apps
Frida hooking
Conclusion
Understanding an STP Root Bridge Election Example is essential for building stable and efficient networks.
By mastering:
- Bridge ID
- Priority
- Election process
…you gain full control over network behavior.
👉 Final Author Insight:
The difference between a stable and unstable network often comes down to proper STP configuration and root bridge planning.
FAQs
What is an STP root bridge election example?
It demonstrates how switches compare priority and MAC address to select the root bridge.
What is STP root bridge priority?
It is a value used to determine which switch becomes the root. Lower values have higher priority.
How is the root port selected?
It is selected based on the lowest cost path to the root bridge.
What happens if priorities are equal?
The switch with the lowest MAC address becomes the root bridge.
Why is STP important?
It prevents network loops and ensures stable communication.
